Your SPRS Score Is a First Impression. Make Sure It’s an Honest One.
Published by DTC Inc. | Cybersecurity & Compliance Resources for Defense Contractors
This article explains what a Supplier Performance Risk System (SPRS) is, how defense contractors and subcontractors submit it for CUI compliance under NIST SP 800-171 and DFARS 252.204-7019/7020, and why CMMC pressure is making sloppy self-assessments a bad bet. If you handle CUI, your SPRS entry is not busywork. It is part of how primes and DoD buyers decide whether to trust you.
Let’s get to the part that matters.
If your company touches Controlled Unclassified Information (CUI) and works in the defense space, your SPRS score exists in a government database right now. Or it doesn’t, which is its own problem. Either way, contracting officers can pull it before they decide whether you’re worth a conversation.
This is not paperwork that disappears into a file cabinet. SPRS creates a visible record of your cybersecurity posture, and that record can matter in source selection, subcontractor vetting, disputes, and enforcement. If you submit or affirm information that your team cannot support, the downside is not theoretical.
At DTC, we see the same SPRS issues come up repeatedly with small defense contractors:
- A lot of them don’t know their score.
- Some never submitted one.
- Others submitted a score that sounded reasonable at the time but wouldn’t survive a third-party audit.
Each of those situations can be fixed (yay solutions!), but the third in particular, creates the most serious exposure because it turns a compliance problem into a credibility problem.
So let’s talk about what SPRS actually is, why the stakes are higher right now than they’ve ever been, and the 10 controls that move scores forward the fastest — without you having to boil the ocean or fake anything.
What Is SPRS?
The Supplier Performance Risk System (SPRS) is a DoD procurement platform that pulls together supplier risk data, including pricing history, past performance, and cybersecurity stance, all into one place for acquisition professionals to use when evaluating contractors.
The cybersecurity component is what defense contractors typically deal with first. Under DFARS 252.204-7019 and 252.204-7020, any contractor that handles CUI is required to:
- Conduct a self-assessment against the 110 controls in NIST Special Publication 800-171
- Calculate a score using the DoD’s Assessment Methodology
- Submit that score to SPRS through the Procurement Integrated Enterprise Environment (PIEE)
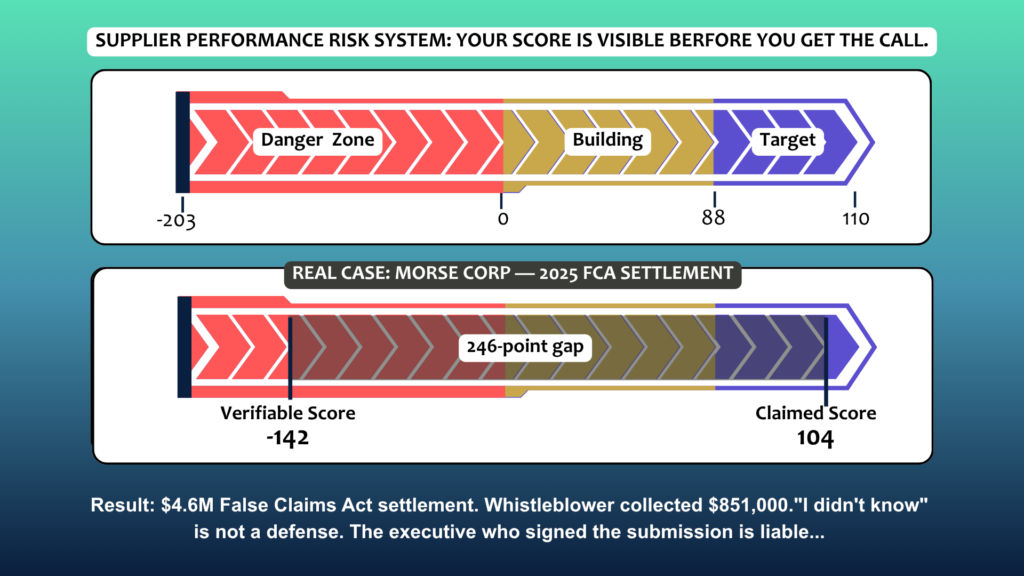
Here’s how it works: The score runs from +110 (every control fully implemented) down to -203 (nothing implemented; yes, it can go negative). Each control carries a deduction of 1, 3, or 5 points based on how much security impact it has.
Pro-tip: Be prepared to support “implemented” with evidence. If a requirement isn’t implemented, it’s a deduction.
Your score goes into SPRS alongside your System Security Plan (SSP), Plan of Action & Milestones (POA&M), assessment date, and scope details. Contracting officers can see it. So can prime contractors vetting their subs. That context matters.
Scoping note (don’t skip this): A surprising number of weak SPRS outcomes start with a scoping mistake, not a technical one. Be precise about which users, devices, systems, cloud services, enclaves, and data flows are actually part of the CUI environment. If your SSP describes one boundary and your operations reflect another, the score may be calculated correctly and still fail to represent the real risk.
Why It Matters More Right Now
While SPRS has been around for a while, the surrounding enforcement has been evolving.
- CMMC 2.0 is no longer theoretical. The CMMC Program Rule (32 CFR Part 170) is in effect, and DoD is phasing CMMC requirements into contracts via the DFARS CMMC clause. In the meantime, acquisition teams and primes can still use SPRS data when screening vendors. Treat a missing or stale record as a preventable competitive disadvantage.
- If you’re a sub, your score is your prime’s problem too. DFARS 252.204-7020 requires prime contractors to verify that every sub handling CUI has a current SPRS score, no older than three years. Primes are not going to risk their contracts over a sub who hasn’t done their homework. You will get cut from the team.
- CMMC Level 2 “Conditional” status has specific scoring + POA&M limits. Under the CMMC Program Rule, an organization can only receive a Conditional Level 2 status if (among other constraints) its score is at least 80% (i.e., the assessment score divided by the total Level 2 requirements is ≥ 0.8) and any POA&M items are limited to certain low-point requirements (with narrow exceptions). In other words: you can’t “POA&M your way out” of major gaps, and you should treat high-value controls as day-one requirements.
- The DOJ has decided cybersecurity fraud is worth its time. In fiscal year 2025, a record 1,297 whistleblower lawsuits were filed under the False Claims Act, shattering the previous year’s record. Cybersecurity misrepresentation is a growing piece of that. These are not hypotheticals:
- MORSE Corp (2025): Self-assessed at 104. Third-party audit found the real score was -142. They paid $4.6 million. A whistleblower inside the company got $851,000 of it.
- Penn State University (2024): $1.25 million settlement for submitting inflated SPRS scores across 15 DoD and NASA contracts. Brought down by a former CIO.
- Health Net Federal Services (2025): $11.25 million for falsely certifying compliance while internal audits were flagging serious gaps. They kept certifying anyway.
- Raytheon / RTX Corporation / Nightwing (2025): $8.4 million to resolve allegations relating to non-compliance with cybersecurity requirements across 29 contracts/subcontracts (including allegations tied to required security planning and safeguarding expectations).
The executive (or designated affirming official) who signs/affirms what’s submitted should assume it can be scrutinized later. Under the False Claims Act, “we didn’t know” may not help if the facts show the organization acted knowingly or recklessly. Also, “we planned to fix it” isn’t a substitute for accurate, supportable reporting.
The 10 Controls That Move SPRS Scores the Fastest
Here’s why these controls matter so much to the score: the DoD assigns each of the 110 NIST SP 800-171 requirements a value of 1, 3, or 5 points. You begin at 110 and subtract for anything not implemented. Roughly 15 controls are worth 5 points each, so resolving a relatively small number of high-value gaps can materially change the outcome.
The most practical approach is to prioritize the highest-value deficiencies first. These 10 controls are often where small defense contractors can improve their score the most without overhauling every part of the environment at once.
1. MFA for All Privileged Accounts: 5 points
Privileged access protected by only a password remains one of the most common and most consequential failures in NIST 800-171 assessments. If administrators or other high-privilege users can reach sensitive systems without MFA, you are giving up five points and leaving a high-impact weakness in place.
Source: NIST SP 800-171 Rev 2, Control 3.5.3
2. MFA for Remote Access: 5 points
This requirement applies to all remote access paths, not only administrator logins. If users can connect to the environment remotely through a VPN or similar method without MFA, the control is not met. For many organizations, this is a relatively straightforward five-point fix.
Source: NIST SP 800-171 Rev 2, Control 3.5.4
3. Limit Access to Authorized Users and Functions: 5 points each
Access control failures tend to create both large score reductions and large audit concerns. Least privilege requires more than a policy statement. It requires documented, enforced limits so users receive only the access needed for their role, and evidence that those limits are actually operating in practice.
Source: NIST SP 800-171 Rev 2, Access Control Family
4. Encrypt CUI in Transit: 5 points
Any CUI moving across a network (email, file transfers, cloud tools) must be encrypted using FIPS-validated mechanisms. Sending CUI over standard email is a direct violation. If your team is emailing sensitive government information without encryption, this is one of the easiest five-point gaps to close and one of the most legally exposed.
Source: NIST SP 800-171 Rev 2, Control 3.13.8
5. Control How Maintenance Is Performed on CUI Systems: 5 points
If your IT vendor is remoting into your systems with an uncontrolled tool, no session logging, and no MFA, that’s a five-point deduction and a real security problem. Remote maintenance on systems containing CUI must use managed, documented sessions that are terminated when work is complete. “My IT guy has TeamViewer” is not compliant.
Source: NIST SP 800-171 Rev 2, Control 3.7.5
6. Establish and Maintain Audit Logs: 3 points each
Meeting this control means more than having logs enabled on a few systems. You need logging that captures relevant activity across the in-scope environment, retains it for an appropriate period, centralizes it where needed, and shows that someone is reviewing it. In assessments, the evidence trail matters as much as the setting itself.
Source: NIST SP 800-171 Rev 2, Audit and Accountability Family
7. Build and Maintain a System Security Plan: 3 points
The SSP is the backbone of your entire SPRS submission. It has to describe every in-scope system, explain how each of the 110 controls is addressed, and define the boundaries of your CUI environment. It’s not a one-pager. Without a current, accurate SSP, your assessment can’t be completed and your score can’t be submitted. This is not a documentation technicality. It was a key issue in several recent enforcement actions and should be treated as foundational.
Source: NIST SP 800-171 Rev 2, Control 3.12.4
8. Maintain a Plan of Action and Milestones: 3 points
A POA&M lists every control you haven’t implemented yet, what you’re going to do about it, who owns it, and when it’ll be done. It’s not an admission of guilt; it’s proof that you understand your gaps and are working them. An accurate POA&M with realistic dates is required for SPRS submission and tells a contracting officer you’re being straight with them. A missing or fake POA&M tells them the opposite.
Source: NIST SP 800-171 Rev 2, Control 3.12.2
9. Identify and Fix System Flaws Promptly: 3 points
This is patch management, but documented, process-driven patch management, not “we get to it eventually.” You need a defined process for identifying vulnerabilities, a window for applying updates, and records showing it’s actually happening. If your approach is reactive and informal, this control is not met, and you’re losing three points you could have kept.
Source: NIST SP 800-171 Rev 2, Control 3.14.1
10. Control and Monitor Remote Access Sessions: 3 points each
Remote access should move through managed points of entry, with defined restrictions on session activity and records showing what occurred. A VPN by itself is not enough if there is no monitoring, no limitation on use, and no evidence of oversight. This is where many organizations discover that remote connectivity and controlled remote access are not the same thing.
Source: NIST SP 800-171 Rev 2, Access Control Family
What “Accurate” Actually Means
Three Things You Need Before You Touch the Submit Button
Before anything goes into SPRS, you need:
- A current System Security Plan (SSP): documenting every in-scope system and how each control is addressed
- A Plan of Action & Milestones (POA&M): documenting every gap, with owners and target dates
- A calculated score: built from the DoD Assessment Methodology, starting at 110, deducting for every unimplemented control
If you don’t have all three, you’re not ready. Submitting without them doesn’t make you ahead of the curve; it makes you exposed.
Where DTC Comes In
DTC is a managed IT and cybersecurity provider with more than a quarter century of experience helping small and medium sized businesses stay safe and thriving. We love IT. And we love people. We’ve made it our prerogative to understand the expectations that come with CUI, the realities of SPRS scoring, and the difference between a score that can be defended and one that creates avoidable risk.
Our role is not to hand over a template and leave you to sort it out. We help you determine where the score stands today, identify the deficiencies that matter most, and build a remediation plan that matches the environment you actually operate.
If you have never submitted a score, have concerns about one already in SPRS, or have not revisited it recently, this is the right time to review it before an acquisition team or prime contractor relies on it.
Talk to DTC about your SPRS score.
Sources: SPRS Official Site | DFARS 252.204-7019 | DFARS 252.204-7020 | NIST SP 800-171 Rev 2 | Clark Schaefer Consulting — FCA & CMMC | Holland & Knight — FY2025 FCA Statistics | PreVeil — SPRS Score Guide | Workstreet — SPRS Guide